What is Pentesting? A Beginner's Guide to Ethical Hacking and Pentesters
Learn what pentesting is, what pentesters do, the tools and skills that matter, and how to start with hands-on practice and certs. Train with Cybrary.
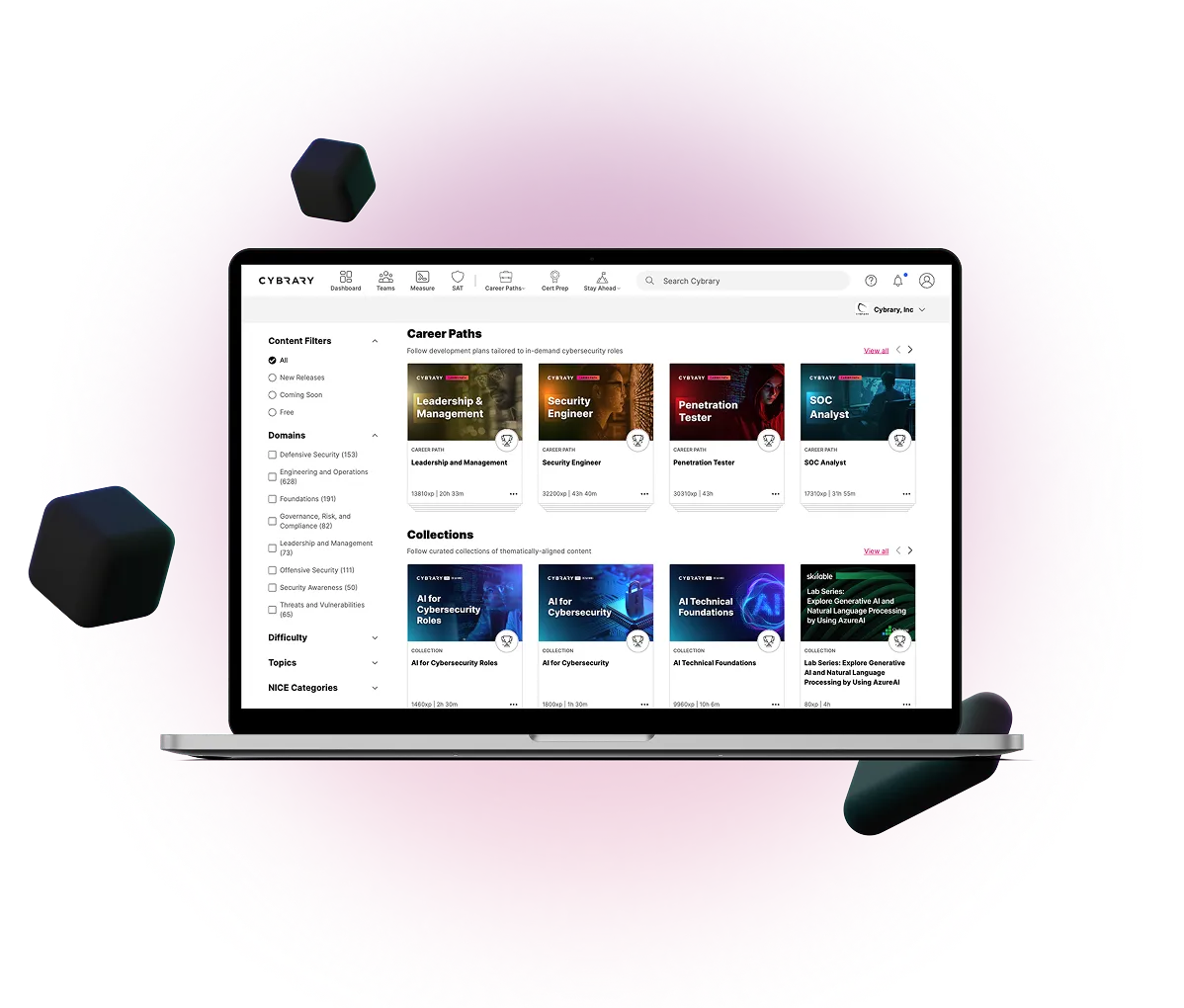
Cybrary’s hands-on cybersecurity training courses and interactive labs empower professionals to stay ahead of threats and save on certification costs.
Trusted by leading organizations worldwide


Don’t settle for generic AI trainings or how-to videos - enable your team with an expert built curriculum. From implementing guardrails to specialized role-based training , gain the knowledge required to design, deploy, and utilize AI successfully and securely.
Build a secure workforce with security awareness training, phishing simulations via CanIPhish, hands-on learning labs, and certification content. Meet your employees where they are with content and paths to fit every role, goal, and skill level.


Whether you’re launching your career or leveling up, Cybrary’s hands-on, expert-led cyber security training builds the essential skills to detect and respond to today’s complex cyber threats. Gain the confidence and credentials you need to grow your cybersecurity career.
Upskill your team with Cybrary’s suite of cybersecurity training, learning activities, and management tools, including hands-on Virtual Labs, role-aligned Career Paths, and personalized remediation. Request a demo and learn how Cybrary tailors our deep library of training to your team’s unique needs.

Jump start your career in cybersecurity with Cybrary's deep training library. From role-aligned career paths to comprehensive certification prep programs, we have everything you need to get ahead and stay ahead in your career. Sign up for a Free account today to start learning today.


In this course, you will learn the basics of defensive security and cyber risk. You will review foundational risk management concepts such as calculating risk and strategies for dealing with risk. You will also explore the NIST CSF as a framework for understanding defensive security.

In this course, you will learn the basics of defensive security operations. You will review the key roles and responsibilities within a Security Operations Center (SOC), as well as enabling technologies for defensive security, including a deep dive on Continuous Monitoring.

CompTIA’s Security+ is a globally recognized certification that equips IT professionals with cybersecurity principles and security best practices, and is often used as a requirement for entry-level cybersecurity positions. This certification prep path is designed to provide you with a comprehensive overview of the concepts and skills you will need to pass the certification exam.

Our Kali Linux certification course and training is designed for those interested in penetration testing and ethical hacking. Kali Linux course is a great place to start your Kali Linux training to learn about the industry-standard tool for penetration and security testing. This is a foundational course that is designed to provide the basics of Kali distribution, installation, troubleshooting, and navigation.